602-448-9676
vCiSO Information Security Consulting
Achieve Resilient & Strategic Security Planning & Governance for Your Organization
A comprehensive approach to strengthening your business security with our virtual Chief Information Security Officer's (vCiSO) Advisory Services. Our vCiSO collaborates with you to develop robust business continuity and incident response plans, vendor/security audits, and vulnerability scans to ensure minimal disruptions and swift recovery. Leverage this highly certified expertise for risk management and security guidance tailored to your organization's unique needs.
Prioritize Security to Propel Your Business Forward
You are concerned for the security of your business assets as you understand the crucial role secure information and data plays in fostering success in today's digital landscape.
Determined to address potential risks associated with inadequate security measures, you are committed to safeguarding your business's physical and digital assets with utmost care and diligence. You recognize the importance of cultivating a security-conscious culture among your employees and vendors.
Embrace the guidance of certified information security experts to reinforce your business's security, mitigate potential losses, and unlock its full potential in a fast-paced, competitive environment.


Your (CISSP) virtual Chief Information Security Officer is Here to Guide Your Business
Gain invaluable insight and guidance for your business’ security from a performance-driven Virtual Chief Information Security Officer (vCiSO) with with an impressive CISSP certification and years of dynamic experience.
Your vCiSO serves as a valuable board-level resource, seamlessly integrating with your organization to oversee security strategy & planning, security budgeting, regulatory programs, and risk assessments.
Collaborating closely with you and your team, your information security officer will devise a strategic action plan, ensuring your business is fortified against threats and vulnerabilities both inside and outside your network.
Achieve Business Continuity & Security with Our vCiSO Driven Process

Risk Assessment
Comprehensive Threat Evaluation: Your vCiSO conducts a thorough risk assessment of your business to identify security vulnerabilities. This vital first step enables effective prioritization and resource allocation to tackle pressing concerns.

In-Depth Analysis
Findings Review: Your vCiSO presents a detailed analysis of the findings, highlighting vulnerabilities that require immediate attention. This comprehensive evaluation empowers your organization to address security gaps effectively.

Action Plan
Tailored Security Roadmap: Your vCiSO develops a strategic action plan and robust business continuity plan to minimize disruptions and ensure swift recovery. This approach reinforces your security posture and aligns with industry best practices.

Business Continuity
Ongoing Improvements: Your vCiSO conducts regular reviews, tracking the progress of security initiatives and the effectiveness of your business continuity, keeping your organization prepared for evolving threats and disruptions.
Your vCiSO is Ready to Help
Secure your business digitally and physically.
or call us at 602-448-9676
The Risks of Neglecting Security Measures
Operating your business with weak security exposes it to significant risks, potentially leading to revenue losses and even personal liability.
Without guidance on implementing established security best practices, your business remains vulnerable in an environment of ever-evolving and sophisticated threats.
Ignorance is not bliss in the realm of security. Recognizing the need to bolster your security strategy, yet lacking the necessary expertise, leaves your business at risk in an increasingly perilous digital landscape.


Reap the Rewards of a Secure Business
Your Security Officer collaborates with you to thwart unauthorized access, disclosure, disruption, and destruction of sensitive data, effectively preventing information security catastrophes.
Empower your employees and vendors to handle sensitive information with utmost care and discretion, protecting the foundations of your business.
Experience peace of mind, and business continuity, knowing your company operates with robust security measures in place, freeing you to concentrate on business growth and expansion.
Call us now at (623) 303-9474 or SCHEDULE YOUR CALL
(IS) Information Security Service Highlights

vCiSO Consultation
Engage in personalized consultations with your vCiSO, who offers expert guidance on your organization's security strategy. From assessing your current security posture to implementing best practices, your vCiSO will be an invaluable resource in managing threats, optimizing security processes, and ensuring compliance with regulatory requirements and agencies.

Risk Assessment Audit
Undergo a comprehensive risk assessment audit, examining your organization's IT infrastructure, processes, and policies. This in-depth evaluation identifies potential vulnerabilities and high-risk areas, helping prioritize security initiatives and allocate resources effectively, while providing actionable insights and a clear understanding of your security posture..

Incident Response Plan
Develop a well-defined incident response plan with your vCiSO to efficiently detect, contain, and recover from security incidents and breaches. This proactive approach minimizes impact, mitigates risks, and reduces recovery time. Your vCiSO will guide you in creating a tailored plan, covering incident identification, communication protocol, containment strategy, and analysis.

Penetration/Compliance Scan
Experience thorough assessments with a combination of comprehensive penetration testing and NIST-CSF scans. Our experts simulate real-world cyberattacks to identify vulnerabilities and assess your defenses. NIST-CSF scans evaluate your organization's alignment with the NIST Cybersecurity Framework's best practices, ensuring compliance with industry standards.

Physical Security Assessment
Assess the effectiveness of your organization's physical security measures to prevent unauthorized access, theft, or damage. Your vCiSO will evaluate the security of your premises, pinpoint vulnerabilities, and provide suggestions to protect your vital assets and staff. This comprehensive review ensures robust security to safeguard against digital and physical threats to your business.

Business Continuity Plan
Establish a strong security infrastructure to ensure continuous operation of vital business functions, even during unforeseen disruptions like cyberattacks, natural disasters, or equipment failures. This forward-thinking strategy minimizes downtime, ensuring your organization remains agile and well-prepared for unexpected events.

“We felt it was very important to not only understand our systems from the view of a third-party looking in but also to be able to create a roadmap to address what we need to work on.”
Duane Wilkes - CFO, Berge Automotive Group
Related Blog Articles
How Do HIPAA Fines Happen — and How Can Proper IT Prevent Them?
HIPAA fines often come from preventable gaps: unencrypted lost devices, weak access controls, missing risk assessments, and poor documentation. Proper IT reduces risk with encryption, MFA, firewalls/E... ...more
Onlinebusiness
March 13, 2026•1 min read

What Are the Most Common IT Mistakes Small Medical Offices Make?
Small medical offices often make avoidable IT mistakes: break-fix support, untested backups, weak passwords/no MFA, skipped patching, assuming HIPAA is “handled,” no incident response plan, and underi... ...more
Onlinebusiness
March 11, 2026•2 min read

Is Local IT Support Better Than National MSPs for Medical Offices?
Local IT often fits small medical offices (5–15 staff) better: faster onsite response, stronger accountability, and better workflow/HIPAA familiarity. National MSPs offer scale but may be remote-first... ...more
Onlinebusiness
March 09, 2026•2 min read
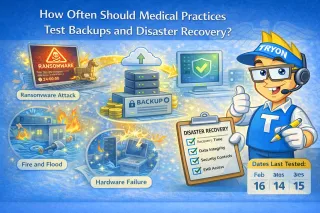
How Often Should Medical Practices Test Backups and Disaster Recovery?
Medical practices should verify backups monthly, run restore tests quarterly, and review disaster recovery annually. Untested backups often fail due to corruption or config changes. HIPAA expects reco... ...more
Onlinebusiness
March 06, 2026•1 min read
How Do Medical Offices Recover from Ransomware Attacks?
Medical offices recover from ransomware by isolating infected systems, assessing impact and entry point, restoring from secure encrypted offsite backups (prioritizing EHR), hardening security (patches... ...more
Onlinebusiness
March 02, 2026•1 min read
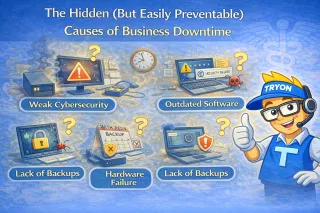
The Hidden (But Easily Preventable) Causes of Business Downtime
Downtime is usually caused by everyday issues—spills, deleted files, bad updates, or aging hardware—not big disasters. The real cost comes from slow recovery. Fast restores, backups, and quick device ... ...more
Backups
March 01, 2026•4 min read
Get started securing your business.
Call us at 602-448-9676 or schedule your discovery call with Tryon Computers, today!
Join Our Community
Stay Connected
Learn
Blog
Events
All Resources
About Us
Who We Are
Our Approach
Careers
Service Area
© 2024 Tryon Computers llc | Terms of Use | Privacy Policy